DevSecOps: The Future of Secure Software Development
In the modern digital era, the demand for rapid software delivery is at an all-time high. Businesses strive to bring new features and applications to market faster than ever to stay competitive. However, this accelerated pace can sometimes compromise the security posture of applications, exposing organizations to costly breaches and compliance violations. This is where DevSecOps comes in—a cultural and technical evolution that integrates security directly into the Software Development Lifecycle (SDLC), ensuring secure, efficient, and continuous delivery.
Introduction
In the modern digital era, the demand for rapid software delivery is at an all-time high. Businesses strive to bring new features and applications to market faster than ever to stay competitive. However, this accelerated pace can sometimes compromise the security posture of applications, exposing organizations to costly breaches and compliance violations. This is where DevSecOps comes in—a cultural and technical evolution that integrates security directly into the Software Development Lifecycle (SDLC), ensuring secure, efficient, and continuous delivery.
What is DevSecOps?
DevSecOps is a compound of Development (Dev), Security (Sec), and Operations (Ops), and it represents a philosophy and set of practices designed to embed security into every stage of development and operations processes. Traditionally, security has been a siloed function, often coming late in the cycle during lengthy audits or before release. This "security as a gate" approach leads to delays, friction, and vulnerabilities slipping through because fixing issues late is significantly more expensive and time-consuming.
DevSecOps flips this by shifting security left, meaning security considerations are integrated from the earliest stages of design and coding, through testing, deployment, and into production monitoring. It's about empowering developers to own security, making it a shared responsibility across the entire team, not just the security department.
Why DevSecOps Matters
The need for DevSecOps arises from several key challenges that traditional SDLC models fail to address:
- Increasing Complexity & Attack Surface: Modern applications are inherently complex, often built using microservices, containers (like Docker), and serverless/cloud infrastructure. This modularity, while powerful for scaling, significantly increases the potential attack surface. DevSecOps mandates security checks specifically for these new components, such as scanning container images and ensuring proper network segmentation.
- The Cost of Late Remediation: According to industry reports, fixing a security vulnerability in the testing phase costs about 6x more than fixing it during the design phase, and this cost escalates dramatically if the vulnerability reaches production.
- Speed vs. Security Trade-off: Rapid CI/CD pipelines (Continuous Integration/Continuous Delivery) can inadvertently push insecure code live if security is not fully automated and integrated. DevSecOps ensures security checks run at the speed of the pipeline.
- Compliance Requirements: Regulatory standards such as GDPR, HIPAA, and PCI-DSS require ongoing compliance and verifiable audit trails. DevSecOps automates compliance checks and generates continuous evidence, turning compliance into an ongoing process rather than a rushed pre-release checklist.
- Evolving Threat Landscape: Cyber threats are more sophisticated and frequent than ever, with a growing focus on exploiting flaws in third-party libraries and cloud misconfigurations.
- DevSecOps addresses these by fostering a security-first culture, backed by automation and continuous monitoring, enabling organizations to deliver software quickly without compromising security.
Core Principles of DevSecOps
The DevSecOps model is built on five interconnected principles:
- Shift Left Security (Early and Often): Introduce security in the early development phases. This involves threat modelling during design, implementing secure coding standards using linters and IDE plugins, and performing early Static Application Security Testing (SAST) on code commits.
- Automation (The Pipeline is the Enforcer): Security checks must run without human intervention to match the speed of DevOps. Integrate security tools such as SAST, Dynamic Application Security Testing (DAST), and Software Composition Analysis (SCA) directly into CI/CD pipelines. This includes failing the build immediately if critical vulnerabilities are found.
- Collaboration (Security Champions): Break down silos between development, security, and operations teams, encouraging shared responsibility. A key practice is establishing Security Champions—developers within the agile teams who receive specialized training to mentor peers and act as the first line of security defense.
- Continuous Monitoring & Protection: Security doesn't stop at deployment. Use tools like Runtime Application Self-Protection (RASP) to monitor and block attacks on live applications, along with intrusion detection systems and real-time security analytics (Security Information and Event Management - SIEM) to detect and respond to anomalies in production.
- Infrastructure as Code (IaC) Security: Ensure that infrastructure provisioning scripts (e.g., Terraform, CloudFormation, Ansible) are scanned and secured. Tools must check for common misconfigurations like publicly exposed storage buckets or overly permissive IAM roles before they are deployed to the cloud.
Implementing DevSecOps: A Step-by-Step Guide
Implementing DevSecOps is a journey that requires organizational change, not just new tools.
Step 1: Assess Your Current Security Posture
- Start by understanding your existing SDLC and where security checks occur. Identify gaps, bottlenecks, and pain points. Perform a Value Stream Mapping exercise to visualize where security validation can be introduced most effectively.
Step 2: Foster a Security-First Culture
- Training is crucial. Developers need to understand common vulnerabilities like the OWASP Top 10, secure coding practices, and the importance of security testing. Gamification (e.g., internal hackathons) can be an engaging way to build security awareness and skills.
Step 3: Integrate Security Tools into Pipelines
Leverage specific tool categories for targeted checks:
- SAST (Static Analysis): Tools such as SonarQube, Checkmarx, or Veracode scan source code without executing it for vulnerabilities like SQL Injection or Cross-Site Scripting. Best practice: Integrate these as a mandatory check on every pull request.
- DAST (Dynamic Analysis): Tools like OWASP ZAP or Burp Suite simulate attacks on running applications (in a staging or test environment) to find issues related to session management, authentication, and improper configuration.
- SCA (Software Composition Analysis): Tools such as Snyk or WhiteSource detect vulnerabilities and license compliance issues in third-party libraries and dependencies, which make up the vast majority of modern application code.
Step 4: Secure Infrastructure and Secrets
- Implement IaC scanning tools like Terrascan or Checkov to validate configuration files against security policies. Use dedicated secret management tools (e.g., HashiCorp Vault, AWS Secrets Manager, Azure Key Vault) to dynamically inject credentials, avoiding the dangerous practice of hardcoded secrets.
Step 5: Continuous Compliance and Monitoring
- Automate compliance audits and implement SIEM (Security Information and Event Management) and monitoring tools like Splunk or Datadog to detect anomalies, unauthorized changes, and suspicious activities in real time. Set up automatic remediation for known issues, such as automatically killing a container that violates a security policy.
Benefits of DevSecOps

Real-World Example: DevSecOps in Action
Consider a fintech startup building a new mobile payment application and implementing DevSecOps:
- Code Security: Developers use IDE plugins to get real-time feedback on security flaws as they type. They employ a secure coding framework that enforces input validation and proper error handling.
- CI Pipeline Gate: Every code commit triggers a SAST scan (Checkmarx) and an SCA scan (Snyk). If a high-severity vulnerability is found, the CI build fails automatically, preventing the vulnerable code from being merged.
- Infrastructure Security: The application's cloud environment is provisioned via Terraform. A tool like Checkov scans the Terraform code before deployment, catching a misconfiguration like an unsecured database port.
- Secrets Management: API keys and database passwords are never hardcoded; instead, the application fetches them at runtime from a centralized HashiCorp Vault.
- Runtime Protection: Once deployed, a RASP agent is running on the application server. When a malicious actor attempts a novel attack (a zero-day), the RASP agent detects and neutralizes the attack from within the application, providing real-time self-protection.
This layered, automated approach significantly reduces vulnerabilities from design to deployment, allowing the startup to innovate fast while rigorously protecting sensitive customer data.
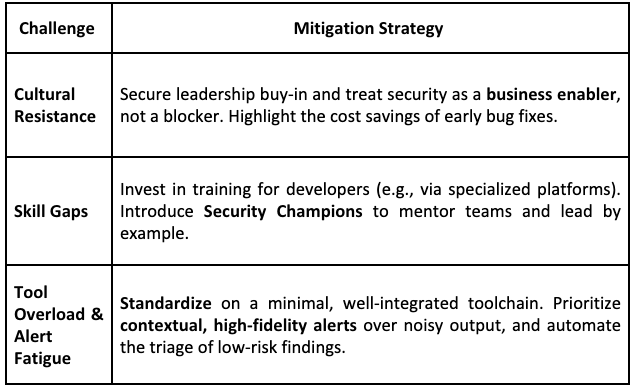
Challenges and How to Overcome Them
The Future of DevSecOps
The DevSecOps practice is a dynamic field. With growing cloud-native adoption, the rise of AI-driven security analytics, and increasing regulatory scrutiny (especially around data privacy), DevSecOps will continue evolving. The focus will be on:
- Platform Engineering: Creating internal, secure-by-default platforms that inherently guide developers toward secure practices.
- AI/ML in Security: Using Artificial Intelligence to perform more intelligent anomaly detection and even suggest code fixes for vulnerabilities.
- API Security: Dedicated tools to test and secure the ever-growing number of internal and external APIs that form the backbone of modern software.
Conclusion
DevSecOps is no longer an optional add-on—it’s essential for organizations wanting to balance speed, innovation, and security in the competitive digital landscape. By embedding security into the very fabric of development and operations, businesses can confidently deliver secure software at scale, safeguarding their reputation, their data, and their customers. The future of software is secure, and that future is DevSecOps.



